New Fraud Schemes: How Cybercriminals Exploit User Trust
In recent months, cybersecurity experts have reported a surge in attacks linked to so-called ClickFix schemes. These tactics rely on social engineering, tricking users into actions that result in malware infections or the theft of personal information. Despite advances in antivirus solutions, the human factor remains the most vulnerable link in the security chain.
Hackers frequently use fake Windows update prompts or bogus CAPTCHA forms to convince users to follow specific steps. As a result, people end up launching malicious code themselves, often without realizing it. These attacks are becoming increasingly sophisticated, and their effectiveness continues to grow.
Concealment Technologies: How Malicious Code Hides in Images
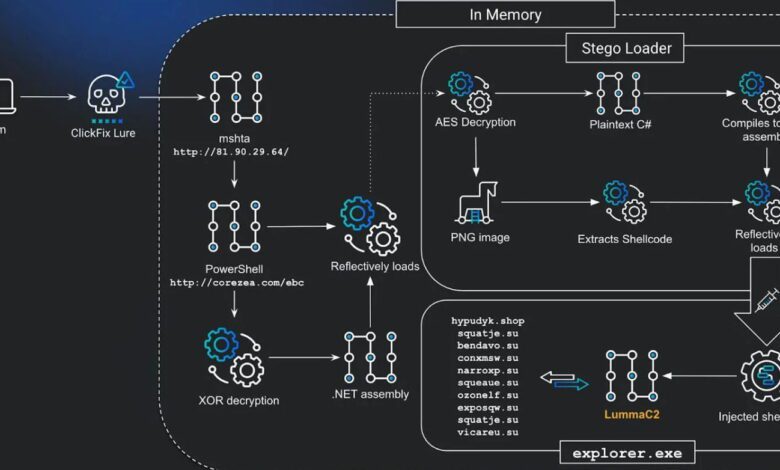
Researchers at Huntress have recently uncovered a new wave of attacks in which scammers use advanced obfuscation techniques. Malicious code is now often embedded inside seemingly ordinary PNG images via steganography. This allows it to bypass standard threat detection tools, since the file appears to be a harmless picture.
During the attack, the user is presented with a full-screen page that mimics a critical system update or a ‘human verification’ check. The screen displays instructions: either enter a specific key combination or paste copied text into the Windows command line. At this point, the malicious script has already placed a dangerous command in the clipboard. Once the user follows these steps, an image containing hidden malware is downloaded to the computer. A special ‘loader’ program extracts and decrypts this code directly in the computer’s memory.
Attack mechanics: How ClickFix works and why it’s hard to detect
The main feature of these new attacks is the use of animations and interfaces that closely resemble real system notifications. The user believes they are solving a technical problem, but in reality, they are launching a malicious process. To further mask its activity, the malicious code calls thousands of empty functions to complicate analysis and slow down antivirus tools.
Even experienced users may not immediately spot the trick, since everything looks familiar at first glance. However, it is precisely this trust in familiar interface elements that makes such attacks so effective. As a result, malware for stealing passwords, spying, or spreading more malicious programs can be installed on the computer.
Who’s at risk and how to protect yourself from new threats
While advanced users are typically able to recognize such schemes, no one is immune to accidentally clicking a malicious link. Those who are not in the habit of verifying the authenticity of system messages or often work with administrative privileges are especially vulnerable. It’s important to remember: no legitimate system will ever require you to paste commands from the clipboard into the console for updates or identity verification.
To minimize risks, experts recommend using up-to-date antivirus solutions, regularly updating your operating system and applications, and paying close attention to any unexpected requests to perform actions on behalf of the system. Avoid clicking suspicious links or downloading files from unknown sites. If in doubt, it’s best to consult a specialist or reach out to technical support.
In case you didn’t know: Huntress and its role in cybersecurity
Huntress is a US-based company focused on developing solutions for detecting and preventing cyberattacks. Founded in 2015, it quickly earned the trust of information security professionals thanks to its innovative threat analysis approaches. Huntress primarily defends small and medium-sized businesses from sophisticated attacks that often bypass traditional antivirus systems.
The company actively researches new hacking techniques, publishes reports on current threats, and develops tools for automated incident response. The Huntress team includes cybersecurity experts with years of experience, among them former government employees and staff from major IT corporations. Thanks to their efforts, many vulnerabilities have been identified and fixed before cybercriminals could exploit them.
Huntress also provides training for users and IT professionals, hosts webinars, and releases educational materials on protection against phishing, ransomware, and other types of attacks. The company collaborates with international organizations and participates in global initiatives to ensure digital security. Its solutions are used in dozens of countries, and the number of clients continues to grow. As of 2025, Huntress is regarded as a market leader in its segment and keeps introducing new technologies to combat cyber threats.











